29-9-2025
H
umans reliance on online platform since covid have increased significantly. Whether it’s purchasing groceries via an application or reviewing bank statements online. Spending hours during the day logging into number of applications and accounts to either pay bills, check our bank accounts or even review our social security benefits. The pressure in trying to remember the user name and password to log into the various portals is exhausting and frustrating
Even if it’s written down somewhere, looking for it and/or going through the process of password rest eats up time and productivity that can be well spent elsewhere.
Take a breath, this service is available and it has proven its success in countries like Saudi Arabia and many Scandinavian counties, it’s the concept of Single-Sign On short for SSO.
The SSO is a federated identity management (FIM) approach , it refers to the authentication process that allows individuals to accesses multiple application with one set of login credentials. Once the individual logs in, there is no need to continue to log in again. It connect the world of various applications using a central services which orchestrates the single sign-on between multiple platforms.
The expansion of technology and internet led to the requirement of establishing a number of accounts. Including shopping, watching videos, completing governmental services, paying bills or even the basic process of checking mails. To sign in into more than one account daily leads to inconvenience and inefficiency. Single Sign-On limits the number of logins individual do, while increase security.
Is It Less Secure?
One might think that one user one password links to less security, exposing the individual information and increasing the opportunity for cyber hacking. The technicality of how it works is not that vulnerable. The main target of cybercriminals is the usernames and the passwords. Each log for an end user into an application and/or websites is a prospect for a hacker. Therefore, with the usage of SSO and entering the user name and password once a day using one set of credentials limits the attacks.
Where The Issue Lays?
About 59%* of individual use either the same or similar password for various account. Making it easy for hacker to access through poorly secured websites. The requirement of user to login in once a day while using on set of credentials reduces the number of attacks. SSO provides a secure the risk of cyber hacking through reducing the attempts of logging in, in turn improving the individual security.
The SSO Protocols
Single Sign-On are assigned authentication tokens when the user first logs in. When entering sites or apps within the same system, the token authenticate the users if the same device is used.
The technical essentials of SSO links with three different entities; the Users, Identity Provider, and Services Providers.
The Users are individuals who need to access different services. Users manage their personal information such as their password, and they it should be uniquely identifiable. The Identity Provider (IdP)provides more information about the User. It is a system that create, manage and provides who this individual is, what role, in turn, inform other systems about what this person is allowed to do. Services Providers (SP) are typically the vendors. They can be either Governmental “National Single Sign-On” and None-Governmental “Single Sign-On”.
Upon the logging of the User in to a SP that uses SSO, the authentication token is released by identifying who is the User is. A verification is created. This token is a all the digital information logged by the user via the browser and or the SSO sever.
Each application that the User logs into will verify through the SSO, in order to pass the token verification request. These tokens are passed through the IdP and SP. It is the job of the IdP and SP to confirm, verify and share the user information.
Three basic protocols: Demonstrated via a diagram:
- Basic Auth: A simple username and password schema on an app, by app basis.
- Open Authorization (OAuth): API security model that relies on an outside Identify Provider and key-store to grant and deny access to APIs.
- Security Assertion Markup Language (SAML) : A web based model that allows a third party application or service to validate the users identity and retrieve details about that user.
The benefits of SSO
Many can argue about the benefits of SSO. Although everyone can agree that SSO is a simple process that provides convenance for end users and with utter-most security.
Improve individual digital experience
There is no requirement for user to apply a number of password for the various applications access. With one password, logging-in once a day allows the user the convince to access a number of application and services limiting the hassle.
Saves time and increases productivity
Due to our reliance on technology, we spend move of our days trying to log into a number of portals to execute the simple tasks during the day. Therefore with one unique user name and password that links the individual’s whole work, it allows for convenience and time well spent.
Decreases IT dependency.
Due to the practicality of SSO, the User log once into the application, limiting the request of IT dependency to rest credentials. Allow IT focus on meaningful tasks, adding value and improving there productivity.
Single Sign-On (SSO) vs National Single Sign-On (NSSO)
Transforming Citizens can access various Governmental services and portals through NSSO back ended with SSO. Granting citizens an authentication services with a single set of credentials to multiple services and applications. This eliminates the need to provides identification to various application.

One of the leading NSSO was released in 2015 by the Ministry of Interior of the Kingdom of Saudi Arabia (the “KSA” ). The application is called Absher. A mandatory applications for all citizens living in Saudi Arabia and well as those visiting the country. Absher, a mobile application that allows citizens and visitors to submit, follow up on online request through various sectors of the governorates in KSA. In Arabic Absher means “Bringing Good News” reflecting the KSA vision of providing its citizens with a seamless and efficient services as well as for the government Ministries and departments.
If you are residing in KSA, it is a requirement for have Absher the official individual eServices mobile application. Providing over 297 services for citizens. Some of these services include banking online, making governmental appointments, all immigration related services including iqama and visa request submissions, all vehicles services and information availability of traffic violations
To setup an account on Absher, individual began the process of registering an account on Absher portal. Upon creating the account, one needs to active it. The activation is done either through Absher Self Services Kiosk Machines or by visiting Jawazat Branches or through ones bank account. An integrated application service.
Absher is the KSA outlets for operation. Enabling citizens and expats practice their daily routines in a seamless and functional way. Without hassles and in a systemic way that links all aspects of life through an application with one user name one password.
An earlier services was released in 2004 in all Scandinavian counties. The BankID. This electronic identification system is in high usage in Sweden. Administrated by Finansiell D-Teknik BID AB, owned by Swedish and Scandinavian banks.

BankID are obtained through any Swedish Bank for Sweden citizens. Links between the citizens, the public and private organization. A citizen through there BankID can accesses governmental e-services, sign documents, full serviced online banking and make payments at e-commerce stores.
The technical infrastructure that BankID follows in regards to operation and maintenance are according to ISO27001:2013. To ensure safety for individuals and eliminate security risk.

Academic Research Enrollment & Judging System for AlQuds Academy
Educational, Nonprofit Organizations
Brand Promotional Website & Doctors Classified for Dry Knight
Educational, Medical, Corporate, Classified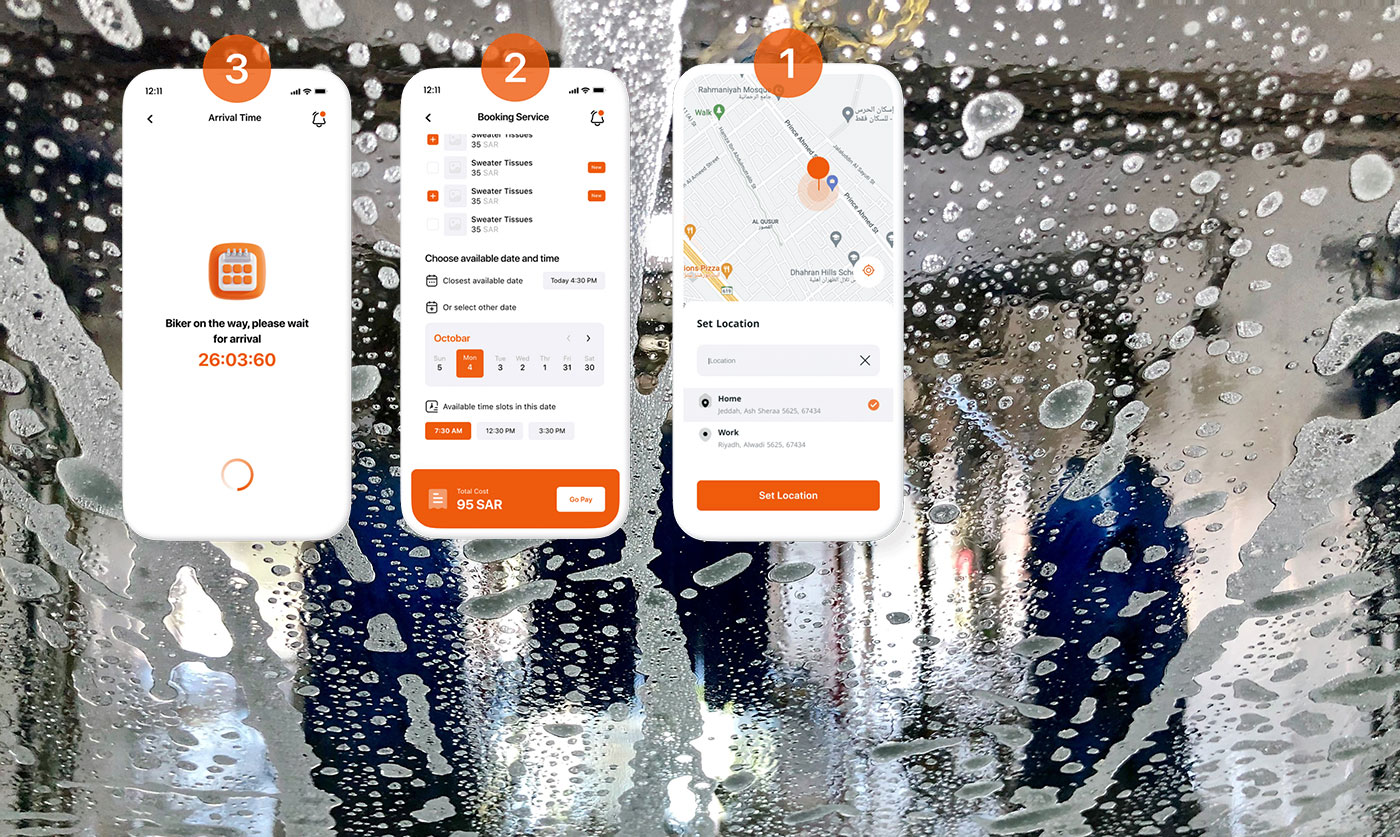
Car Wash Service Aggregator and Provider Applications
Mobile ApplicationRing for mer informasjon og feilsøking
imponert? Kontakt oss for å fordype deg dypere og avdekke mer om det du har vært vitne til. Utvid din kunnskap med oss.
Discover more